So i recently upgraded my wifi at home from a TP-Link to a Mikrotik hAP ac device/s, although the installation of CAPsMAN and provisioning of Configurations were rather quick and easy .. that was not the end.
This post will focus on the wireless connections between the Chromecast and Mikrotik AP.
As in most households these days multiple media devices, wireless speakers/assistants and tablets etc. need the ability to connect ot the wifi.
Below so far my tests and findings with the Google ChromeCast.
I have decided to simplify my SSID's and only have 2 available on the network: Private and Guest and have both bands (2ghz & 5ghz) / radios assigned to the same SSID's. The previous wireless installation had seperate SSID's for 2 ghz and 5 ghz.
Connecting the Chromecast to the network was a breeze, just launch the Google Home application, select devices > settings > Wi-Fi and enter the new credentials.
and then the fun started, family members start complaining they can't "see" the Chromecasr device to cast to, and constant reboot / power cycles started and I started to keep an eye on the Mikrotik log and wireless registration table (and funnily enough all seemed ok, but the user experience were correct the devices were no longer discoverable)
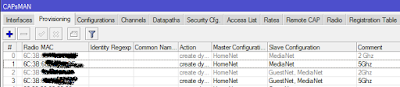
Initial setup:
I then decided to pidgeon hole the Chromecast onto it's own SSID and assign it only to one spesific radio, that way I can control & troubleshoot. I did so and created a Media SSID and assigned it to a radio. This is done by creating a new CAP's provisioning with the target Radio MAC.
Provisioned the new configurations and learned lesson 1, for no money would the Chromecast want to join the new SSID, various other devices could connect to it though.
I changed the configuration in the following order with all configurations experiencing the same result:
Current working configuration:
So currently it seem very stable and working without issues.
It is running for 3 days without any issues so far.
This post will focus on the wireless connections between the Chromecast and Mikrotik AP.
As in most households these days multiple media devices, wireless speakers/assistants and tablets etc. need the ability to connect ot the wifi.
Below so far my tests and findings with the Google ChromeCast.
| Mikrotik Version | 6.37.3 |
|---|---|
| Mikrotik Firmware (hAP ac) | 3.34 |
| Mikrotik Model | RouterBOARD 962UiGS-5HacT2HnT |
| ChromeCast Firmware | 1.22.78337 |
| ChromeCast Model | Chromecast 2 |
I have decided to simplify my SSID's and only have 2 available on the network: Private and Guest and have both bands (2ghz & 5ghz) / radios assigned to the same SSID's. The previous wireless installation had seperate SSID's for 2 ghz and 5 ghz.
Connecting the Chromecast to the network was a breeze, just launch the Google Home application, select devices > settings > Wi-Fi and enter the new credentials.
and then the fun started, family members start complaining they can't "see" the Chromecasr device to cast to, and constant reboot / power cycles started and I started to keep an eye on the Mikrotik log and wireless registration table (and funnily enough all seemed ok, but the user experience were correct the devices were no longer discoverable)
Initial setup:
I then decided to pidgeon hole the Chromecast onto it's own SSID and assign it only to one spesific radio, that way I can control & troubleshoot. I did so and created a Media SSID and assigned it to a radio. This is done by creating a new CAP's provisioning with the target Radio MAC.
Provisioned the new configurations and learned lesson 1, for no money would the Chromecast want to join the new SSID, various other devices could connect to it though.
Lesson learned: I performed a factory reset (FDR) on the Chromecast and it seemlessly connected to the new newly created SSID.
I changed the configuration in the following order with all configurations experiencing the same result:
- Started with band=2ghz-b/g/n with same behaviour
- Changed to band=2ghz-b/g as some people / forums suggested issues with n band, with same behaviour
- Changed to the 5ghz radios with band=5ghz-onlyac, FDR the Chromecast and registered it to the Media SSID.
Current working configuration:
So currently it seem very stable and working without issues.
Media band = 5ghz-onlyac radio = only the closest 5ghz Radio to the Chromecast
It is running for 3 days without any issues so far.
Inconsistencies and possible Chromecast bugs:
- I have one other Chromecast connected to the "Private" SSID without any issues at the moment, still to investigate further.
- On the Google Splash screen the Wireless SSID disappear sometimes with a "backdrop" change (As I told the kids to look for that to determine if the Chromecast is connected or not it causes false negatives at the moment :-) )
Next steps:
- Let it run for a while and monitor.
- Change the Media SSID to hidden.






 [/caption]
[/caption]